


Formstack Sign is the eSignature tool that enables organizations to execute revenue-generating documents—like contracts, invoices, and agreements—easily and securely, ensuring a hassle-free digital experience that impresses end-customers. Formstack Sign is committed to transparent pricing, giving organizations the confidence to move forward without unpredictable costs.



Keep your signing process on track with automated reminders delivered via text and email. Ensure signers stay informed and act quickly, enabling faster completion of revenue-generating documents while maintaining momentum in your processes.


Facilitate efficient collaboration with multi-participant signing, enabling multiple stakeholders to review and execute documents in the order you specify. Whether managing contracts, agreements, or invoices, this feature ensures a structured and timely way to collect more than one signature.


Save time and streamline document preparation with reusable templates. Create and customize templates for commonly used documents, reducing repetitive tasks and ensuring consistency across all your signature requests.

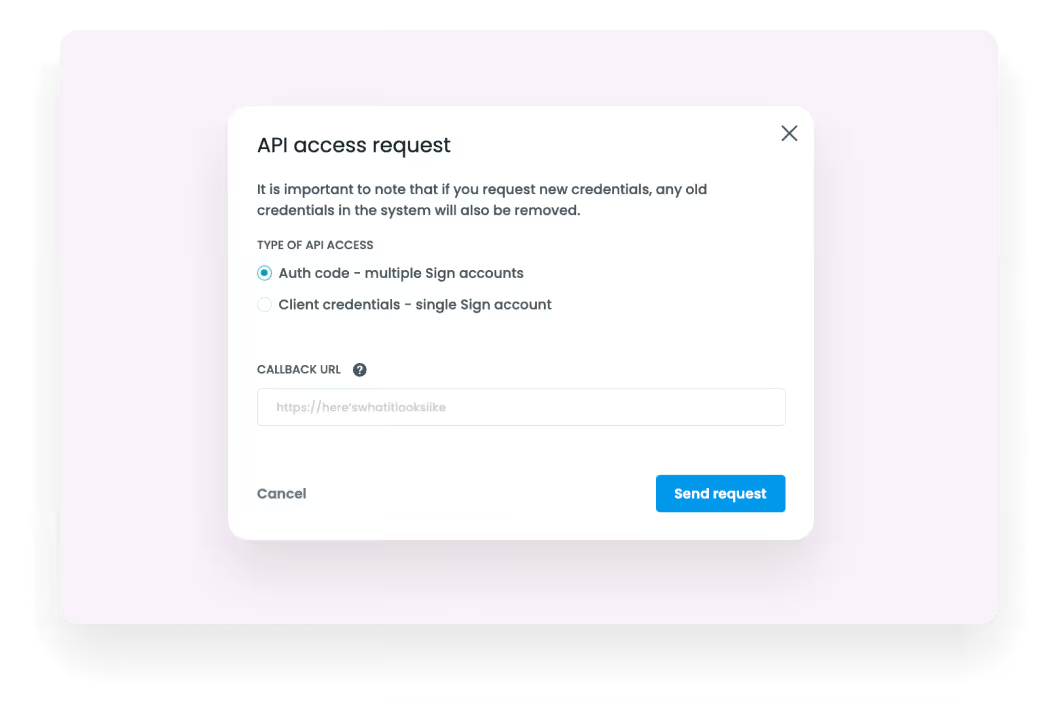
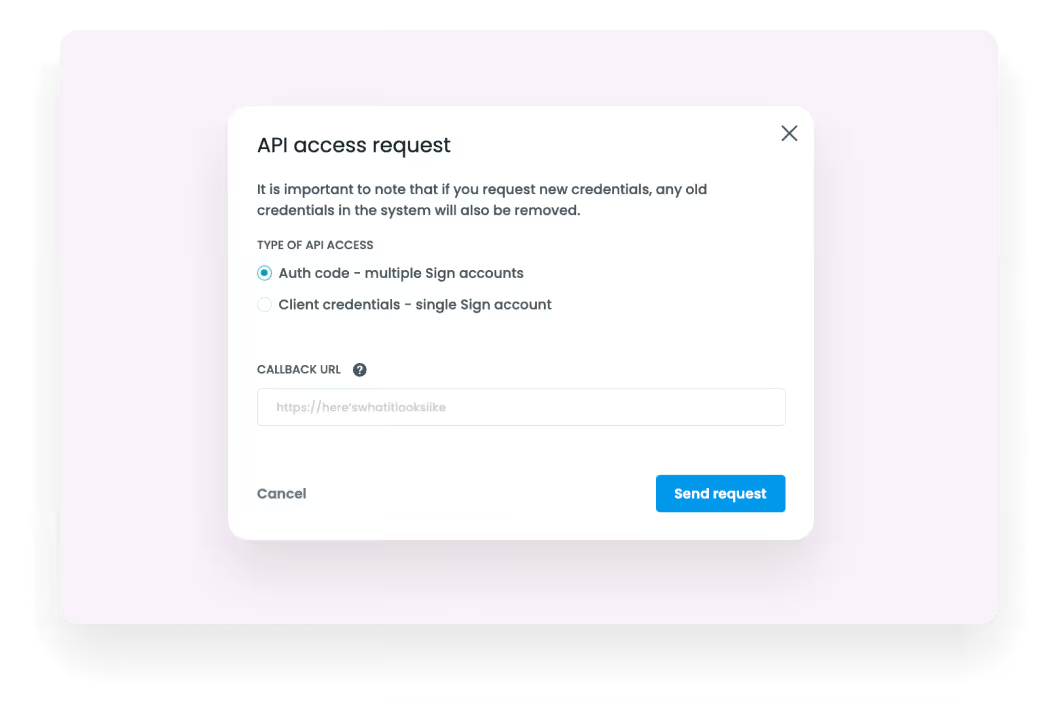
Seamlessly integrate Formstack Sign into your existing systems with our Open API. Build custom eSignature solutions tailored to your unique business needs, ensuring maximum efficiency and scalability.
Pair Formstack Sign with other Formstack products to build end-to-end digital workflow automation.
Automate the entire lifecycle of revenue-generating documents, transforming your raw data into professional, dynamic documents and impressing your end-customers.
Automate data collection to data workflows by using Formstack’s no-code online form builder.

Securely collect and manage data all within your Salesforce org with market-first native-to-Salesforce forms.
